Technology enthusiasts are all too aware of how governments would like nothing more than to snoop on their smartphones. That could be accomplished either by building in backdoors on the software level, or by gaining access to communication logs from popular IM service providers. A new hacking method recently discovered by security researchers takes the form of a secret chip hidden inside replacement parts. For now, this method is known as a chip-in-the-middle attack.
Beware of Chip-in-the-middle Attacks
Very few people would expect government officials to tamper with the hardware components found in their smartphone. It would be very difficult to do so, especially during the manufacturing process. Without consent from the company building these devices, that becomes even more difficult. However, it seems there may be a way of doing so that does not require manufacturers’ permission.
Through what is known as a chip-in-the-middle attack, it is possible for malicious actors to mass manufacture electronic spare parts with hidden chips lodged inside. Every single one of these chips would be able to intercept device communication or execute malicious commands remotely. It is a very dangerous threat, although implementing it feasibly is something else entirely. One needs to have serious manufacturing capabilities to even consider such an attack in the first place.
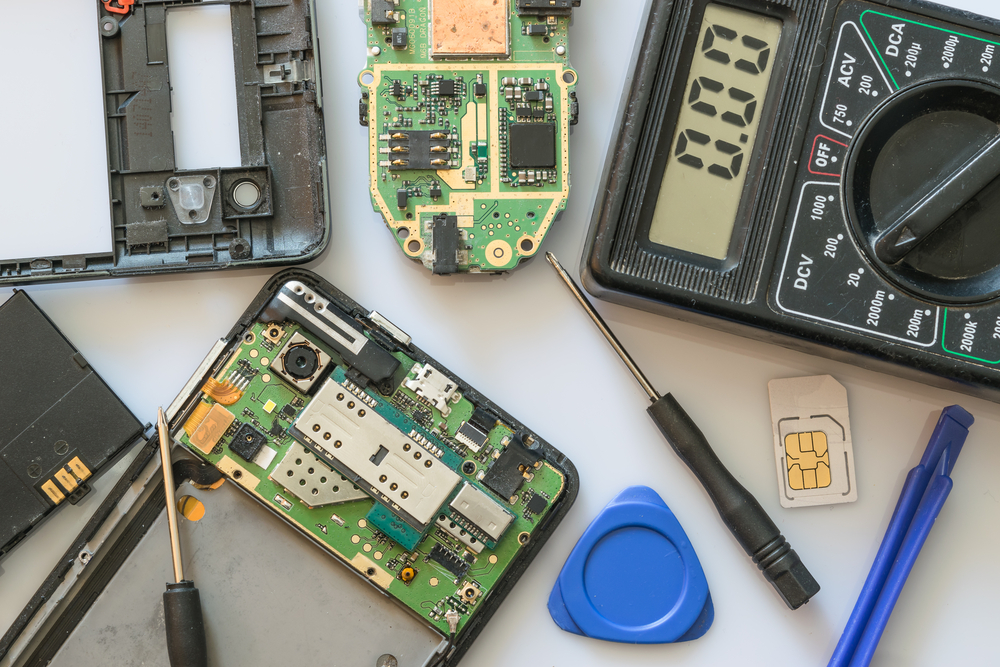
That does not mean it could not be executed successfully. Researchers have proven this by building malicious spare parts and successfully using them to take over a smartphone. During the test, the researchers successfully snooped on communication and even sent malicious commands to the phone in question. It appears such an attack could be launched by buying off-the-shelf electronics which are sold in most stores for US$10 or less. It would require some soldering skills, but it is something that could be done relatively easily.
A lot of people send their phones off to repair shops when something is broken. They generally have no control over the service provided or the spare parts used in the process, and it would be virtually impossible to tell whether or not replacement parts are benign. It is highly unlikely someone would tamper with parts for this particular purpose, although one should not dismiss the possibility either. Stranger things have happened. There are two types of chip-in-the-middle attacks, both of which could have disastrous consequences for the end user.
Thankfully, the researchers documented all of their evidence and published a white paper on the topic. This information needs to be shared with the rest of the world. Far too often, consumers remain unaware of the dangers that lurk beyond their eyesight. Everyone who sends in a smartphone to have parts replaced should be very concerned right now. Although no one has officially built these malicious chips, it is not all that hard to do. Anyone could do it, which is even more disconcerting.
All of this goes to show governments and other malicious actors do not necessarily need to install a software backdoor to get the information they are after. For all we know, every phone manufactured within the U.S. already has such data-stealing chips embedded within them. Most people never open the back of their smartphones other than when they are freshly purchased and require insertion of a SIM card or battery. It will be interesting to see if anyone attempts to pursue this attack vector in the future.