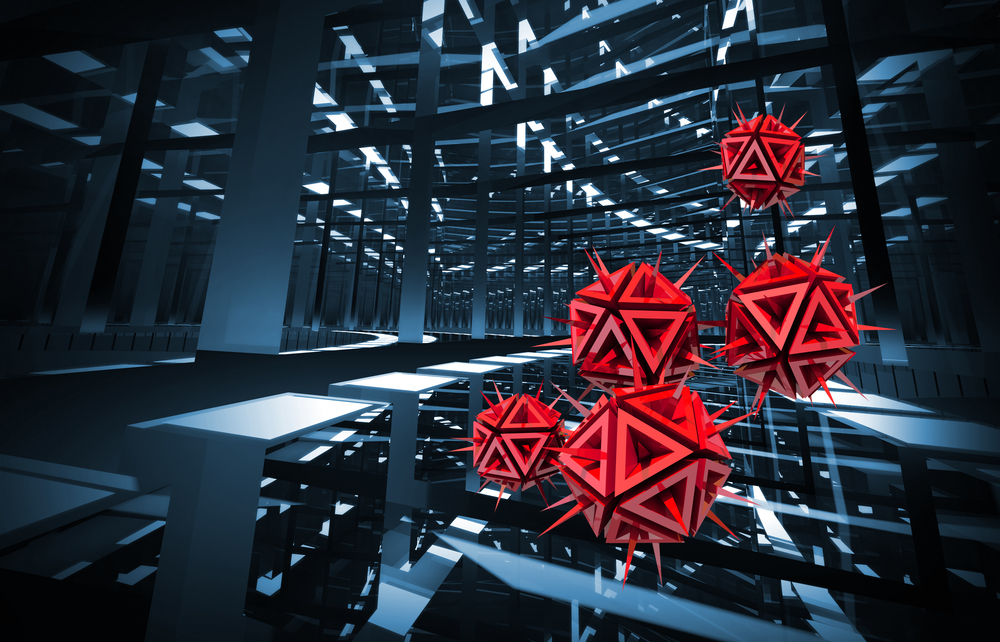
As if the ransomware threat is not dire enough already, it looks like a long-lost version is making the rounds once again. Security researchers came across a new distribution campaign for the VirLocker ransomware. Considering how this malware is capable of copying itself into any infected files, the ransomware can easily spread to other people or be copied onto a removable drive.
VirLocker Is A Nasty Piece of Work
In most cases, ransomware victims can bypass paying a Bitcoin fee by restoring a backup of their data. That is, assuming they made a recent backup not too long before the infection occurred. Unfortunately, that will not be the case when getting infected with VirLocker, as the ransomware strain makes it impossible to use backups. In fact, these backups will become infected as well, which creates a whole new set of problems.
Once a computer gets infected with the VirLocker ransomware, the malware will immediately copy itself into every file it comes across. Removable storage devices connected to the computer at that time – or in the future – have a high chance of receiving a copy of this ransomware as well. Since most cases store hard drive backups on USB sticks or DVDs, it is impossible to use this form of media in a secure manner.
Victims only have one viable option, which is making sure the computer is cleaned up entirely. Unfortunately, that will not be easy, as any downloaded tools will become infected as well. This is one of the primary reasons why security researchers have been so concerned about this malware strain. Even detecting this malicious software is challenging, as VirLocker is more than capable of bypassing most antivirus and anti-malware detection programs.
There is a lot more to VirLocker than just these threats. Its developers keep track of every machine infected and validate whether or not a payment was received from that victim in the past. Assuming that is the case, it will then decrypt and extract the original file embedded within the payload. Users who have not made a payment yet will be greeted with the ransomware message shortly after.
Users who have never dealt with a VirLocker infection before will not notice something is wrong right away. While this malware runs in the background, everything else will remain normal to the computer users. However, the ransomware can easily spread without the device owner ever noticing he or she got infected in the first place. Any activity from that point forward, including sending files to people through social media, will only aid the distribution of VirLocker on a global scale.
Thankfully, there is an easy trick to bypass the payment screen. As soon as victims enter any random 64-length string in the Transfer ID text box, the malware will assume a payment has been received. Afterward, users can decrypt their files one at a time. A very tedious process, to say the least, but it is still far better than paying a sum in Bitcoin. Once all files are decrypted, a fresh install of the operating system is mandatory.
If you liked this article, follow us on Twitter @themerklenews and make sure to subscribe to our newsletter to receive the latest bitcoin, cryptocurrency, and technology news.