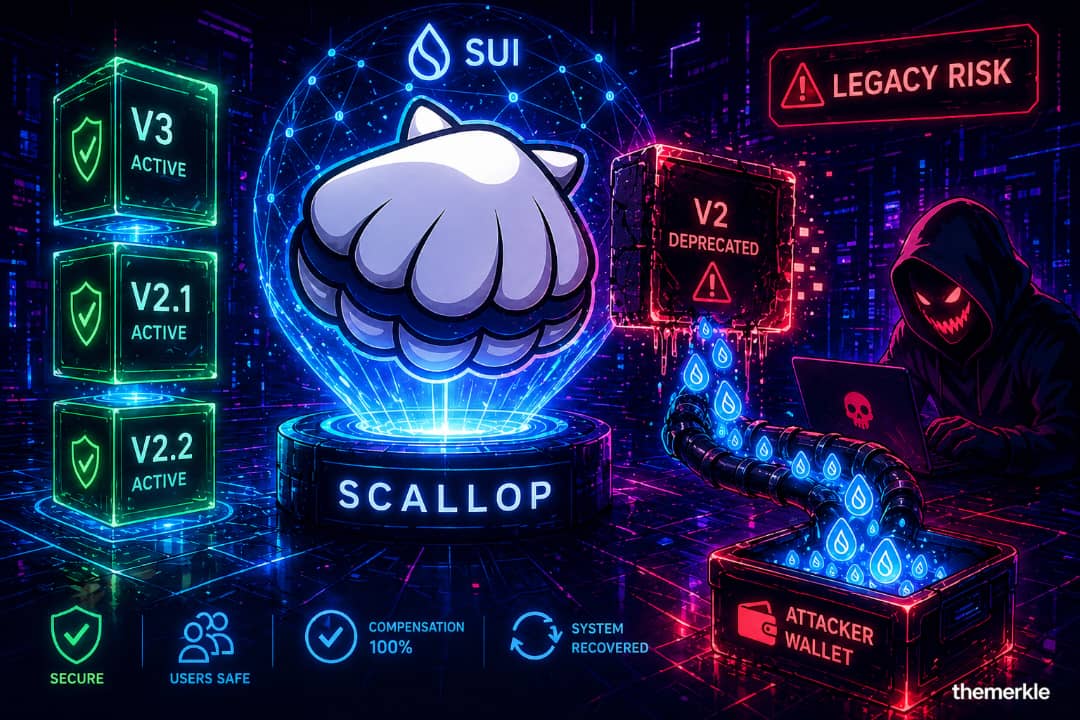
Scallop Confirms Targeted Exploit: 150,000 SUI tokens Siphoned From sSUI Rewards Pool.
The Sui-based DeFi protocol Scallop has confirmed that it was the target of an exploit that drained roughly 150,000 SUI from its sSUI rewards pool while revealing a decades-old bug lurking inside a deprecated smart contract.
As per the official statement of the protocol, they noticed that the attacker disturbed their active codebase and standard SDK interfaces completely. Instead, they called into a deprecated V2 package version that dated back to November 2023, which was still on-chain but sat around unused for months.
Having this level of precision has received a significant amount of attention throughout the ecosystem. This exploit either implies deep reverse engineering or someone had great familiarity with the contract architecture.
Most notably, the vulnerability remained undetected for almost 17 months because the ecosystem moved to new contract versions. Scallop took to Twitter to confirm the incident and said users as of now were safe since immediate containment measures were implemented.
🚨 SECURITY INCIDENT NOTICE
We have identified an exploit affecting a side contract related to Scallop’s sSUI spool rewards pool, resulting in a loss of approximately 150K SUI.
The affected contract has been frozen. Our core contracts remain safe and only the sSUI rewards pool…
— Scallop (@Scallop_io) April 26, 2026
Exploitation of Defective Reward Calculation Mechanism
The exploit shows a critical flaw in the reward calculation logic of the deprecated contract. It uses what’s called a “spool index,” which is an ever-increasing value that represents the total rewards accumulated in that pool over time.
During normal operation, every user account keeps a last_index when they stake. Rewards is calculated on the difference between the index at the moment and the stored value, so that no user can earn rewards before he starts staking.
In the old V2 package though, newly created spool accounts were never initialized; last_index was always zero. And this error provided a major loophole.
Pool Drain Leading To Massive Bouncing Of Points
The results of this bug were instant and dire. The spool index had risen to nearly 1.19 billion over about 20 months. The attacker was rewarded an overblown 162 trillion reward points, set evenly with 136,000 sSUI staked.
Exacerbating this, the rewards pool had a 1:1 conversion ratio so that every reward point converted directly to SUI tokens. This enabled the attacker to seamlessly cash-out points obtained via artificial inflation into real assets.
The exploit led to emptying the rewards pool, which contained about 150,000 SUI at that time. Despite the attacker’s rationalised rewards being far in excess of the pool balance, only on hand liquidity was extracted.
Scallop drained for 150K SUI by someone who knew exactly which deprecated package to call. Not the active code. Not the SDK path. An old V2 from November 2023 that nobody's used in months. Either deep reverse engineering, or someone who knew where to look. The bug had been… pic.twitter.com/jsPE9OCsNJ
— Vadim (AI, ⋈) (@zacodil) April 26, 2026
Immutable Contracts Create a Permanent Attack Surface
This incident illustrates one of the systemic challenges that exist with deployed packages on the Sui ecosystem: deployed packages are immutable. And when a smart contract goes on-chain, it is unable to be deleted or modified. All versions, past and present, remain callable forever.
While Scallop redirected users to a new, safer package through their SDK the old V2 contract was still viewable. The Spooled and RewardsPool objects are shared, so the attacker was able to completely bypass the updated logic because there are no version restrictions on them.
This type of vulnerability, which has been reclassified as a “stale package” risk, brings to light an important blind spot for many DeFi systems. Legacy contracts can be permanent attack vectors because there are no explicit version checks baked into shared objects.
Broader Non-Core Vulnerability Patterns Afoot
The Scallop exploit is an event, not an endless result of a larger trend that has been going on throughout April. Multiple recent attacks have stemmed from not core protocol logic but peripheral or overlooked aspects. Vulnerabilities in RPC infrastructure of KelpDAO, privacy layer (MWEB) for Litecoin and access control bugs in adapter systems from Aethir are just some of the examples.
In all cases, the source was external to the main contract and in other secondary or legacy modules. Usage of such a pattern is indication that adversaries have changed their tactics. Hackers are spending less time on core contracts which get audited a lot, and much more time attacking edges of the ecosystem that have very weak monitoring of their perimeter. This requires a paradigm shift for developers and auditors. Just securing new deployments does not suffice, all the historical contracts, integration points and infrastructure components should be treated as active threat surface.
Full Compensation And Recovery Of The System By Scallop
Scallop used a swift and decisive approach, in responding to the exploit. The attacked contract was immediately frozen in the aftermath, meaning only one rewards pool had been compromised by this exploited attack.
The Group confirmed that the core contracts are still safe and no user deposit has been compromised. Other pools remain untouched and the main functions of the protocol are active as soon as unimpacted pieces unfroze.
Notably, Scallop has pledged to compensate 100 per cent of the losses that have occurred as a result of the exploit. This pledge shows accountability in fixing likely unexpected security holes, and aims to regain user trust.
Deposits and withdrawals have resumed, suggesting system stability has been restored.
Lessons From The World Of DeFi Security
The scallop incident embodies a key lesson for the DeFi ecosystem as a whole. If executing in an immutable smart contract environment, security is never a set-and-forget affair.
Any version of your deployed contract is a part of the live system. Even inactive code can constitute a single point of failure months or years down the road, if proper safeguards are easy to bypass.
Going forward, the ecosystem needs to adopt tougher version control practices, continuous monitoring over legacy contracts and broadening audit scopes to cover all prior deployments. As the exploit shows, attackers are prepared to go deep into a protocol history to find weaknesses they can exploit.
In the end, decentralized finance will become merely as durable as the protocols that can adapt to this changing threat landscape.
Disclosure: This is not trading or investment advice. Always do your research before buying any cryptocurrency or investing in any services.
Follow us on Twitter @themerklehash to stay updated with the latest Crypto, NFT, AI, Cybersecurity, and Metaverse news!