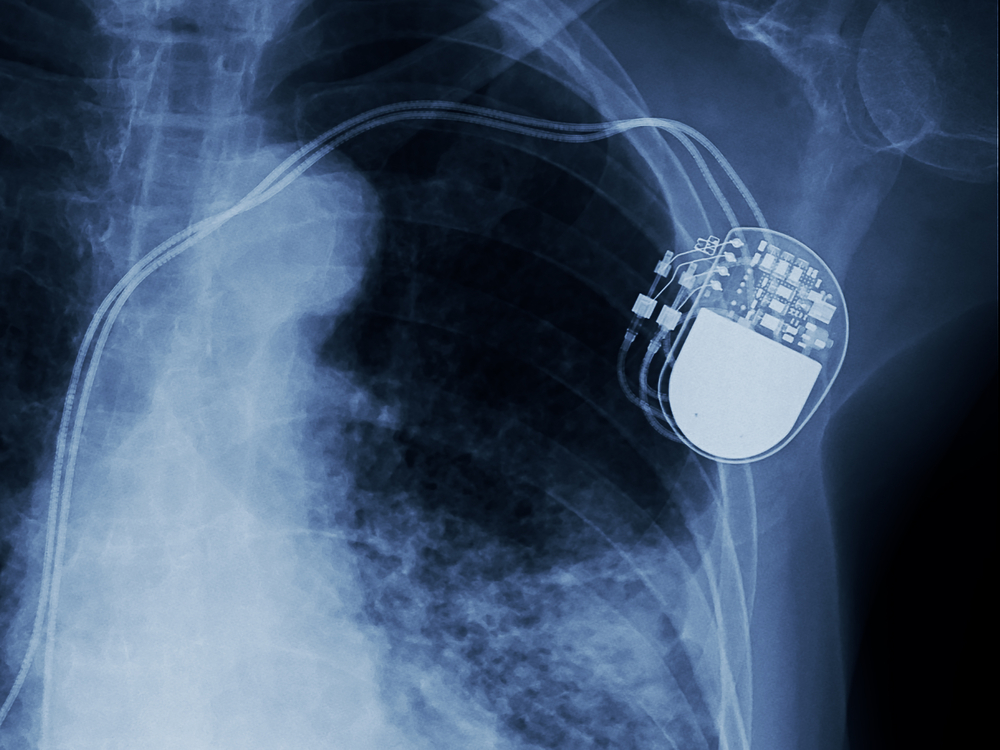
A lot of people around the world rely on a pacemaker to increase their lifespan. Unfortunately, it appears these devices are not safe from harm by any means. A new report by WhiteScope paints a very troublesome picture, as over 8,600 vulnerabilities have been identified. As is to be expected, issues range from smaller code bugs to major design flaws that put patients’ lives at stake.
Pacemaker Vulnerabilities Are Plentiful
It is very troublesome to learn pacemaker devices are susceptible to so many different bugs right now. Medical devices should be the number one type of product that is incredibly difficult to take advantage of. Unfortunately, that is not the case by any means. In fact, it appears pacemakers are perhaps one of the most prone devices to outside attacks right now. That is anything but good news for devices designed to save people’s lives.
With 8,600 flaws discovered by WhiteScope, it is evident something will need to change sooner rather than later. The simple code bugs will be the easiest to fix, as they can be addressed in a firmware upgrade moving forward. What is more troublesome is the design choices so many manufacturers seem to suffer from. Putting patient lives in danger for no good reason is simply unacceptable. Four different manufacturers have been identified as “at risk”, although it is possible these problems extend beyond this scope as well.
One thing that is not surprising by any means is how the majority of vulnerabilities can be found in third-party components and libraries. To be more specific, most devices in the pacemaker category use a cloud-based infrastructure to relay data. Additionally, every pacemaker device comes with its own set of programming libraries, which support the software running on the device itself.
Most of these programming libraries are vastly outdated, which exposes the pacemaker devices to potential remote attacks. It seems rather difficult to ensure these devices have the latest software version support at all times. It is the same as running an older version of an operating system on any device: after a while, they no longer receive security updates. The same applies to outdated versions of programming libraries. Pacemaker programmers will need to step up their game in this regard.
This news does not come as a big surprise to most security experts, though. Implantable medical devices have a bit of a history when it comes to being insecure. In fact, reports like this date back all the way to 2013, and it looks as if the situation is only getting worse. Pacemakers should be properly protected and secured at all times, yet manufacturers are not doing enough to make that happen. Addressing this situation will not be easy, but it is something that needs to be done regardless.
It is evident the medical sector has their work cut out for them. Making devices more safe and secure should be the top priority right now. Knowing one’s pacemaker could be disrupted by a software bug or exploit at any given moment will not put people’s minds at ease anytime soon. The identified manufacturers – who have not been named in the report – will hopefully address all of these problems in the near future. Pacemakers keep people alive, and they should never be susceptible to any software or hardware vulnerability whatsoever.
If you liked this article, follow us on Twitter @themerklenews and make sure to subscribe to our newsletter to receive the latest bitcoin, cryptocurrency, and technology news.