We have touched upon BirkcerBot malware several times already this year. This particular malware is quite nasty as it infects IoT devices and effectively renders them useless. It now appears that the developer of this malware has claimed responsibility for bricking as many as 60,000 Indian modems over the past few months. That is quite a bold claim, but it seems that there is some truth to it after all.
BrickerBot Is a Nasty Piece of Work
BrickerBot is a tool simply designed to cause harm to internet-connected devices, an agent of pure chaos. It has caused a fair bit of damage so far, and it looks like it will not be stopping anytime soon. It appears the developer of this nefarious tool has been trying to generate additional mainstream media attention for his exploits to date. He has now claimed responsibility for a cyber attack causing over 60,000 Indian modems and routers to drop their internet connections.
It is certainly possible the Brickerbot author has bricked a plethora of devices over recent months. His previous attacks have infected thousands of devices as well, so there is no reason to think his future exploits would be less severe. The latest BrickerBot attack affected devices belonging to Bharat Sanchar Nigam Limited and Mahanagar Telephone Nigam Limited, two state-owned Indian telcos.
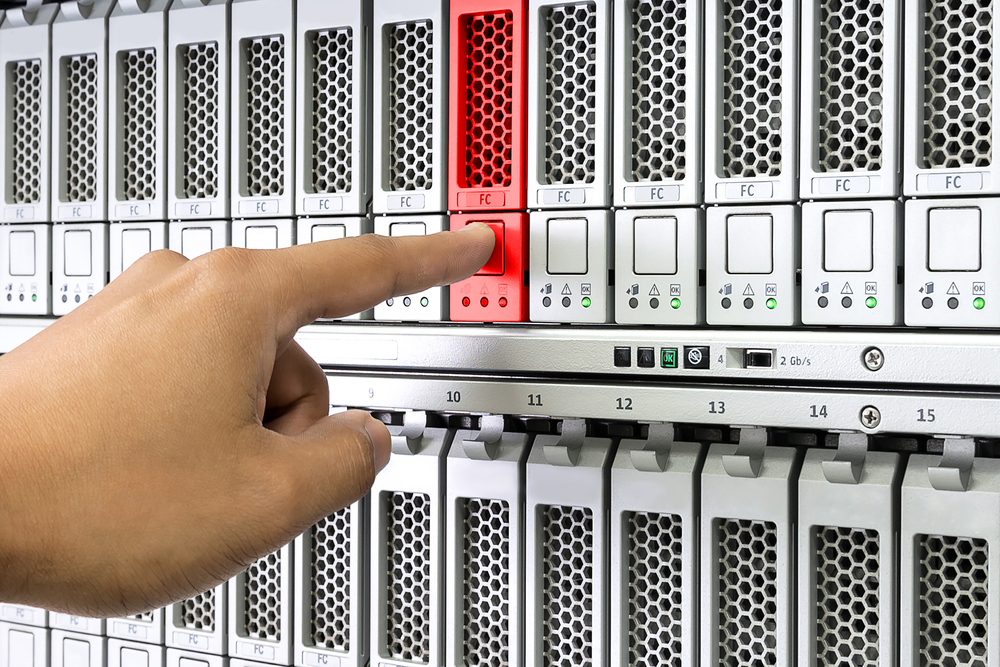
These attacks date back to July 25th of this year, when users of both companies started reporting issues with their internet connectivity. The attacks lasted until July 29th and things got a lot worse over time. The affected users reported that their modems and routers were no longer connecting to the internet and that their devices displayed a red LED at all times. It did not take long for both telcos to figure out this had been a major malware attack targeting their systems. However, solving the matter would be something else entirely.
The 60,000 affected devices represented 45% of all Bharat Sanchar Nigam Limited customers across India. That is a significant number. BrickerBot was successful due to the fact that many users had not changed the default login credentials for their devices. Newly-installed modems were affected as well, but no precise number was ever reported to the public. Device security is not a top priority for most of BSNL’s user base, apparently.
Resetting users’ devices initially appeared to solve the problem. However, even the modems that underwent a successful reset procedure suffered from the same attack again in no time, indicating this fix would not work all that long. Ultimately, a fair few devices had to be replaced. Although it was not officially confirmed that BrickerBot had been responsible for this attack, the malware’s developer certainly claimed that to be the case.
BrickerBot connected to these modems and routers over external port 7547. It appears that both Indian telcos allow remote connections to their hardware over this port. Why that was the case is unclear at this time. The port is used by TR069, a management protocol wielded by ISPs to send commands and manage routers at customers’ homes. Using this port with the default login credentials for this hardware has proven quite disastrous.